File Ap8qs3yamty4.png — Download
Use tools like ExifTool to check for timestamps, GPS data, or the software used to create the image.
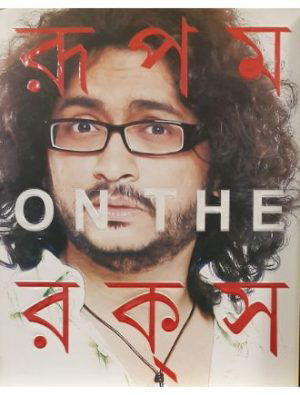
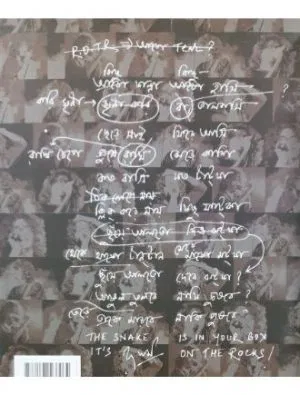
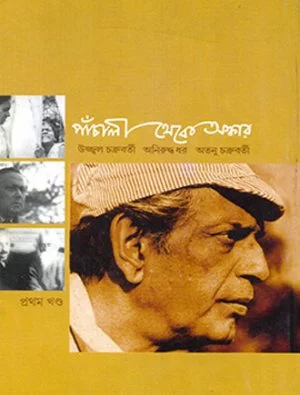
Describe the content—whether it is a screenshot, a diagram, or a photograph. Download File ap8qs3yamty4.png
In cybersecurity "write-ups," such filenames are often part of a digital forensics puzzle where the goal is to extract hidden metadata or reveal a "flag" within the image. Technical Analysis (Write-up Template) Use tools like ExifTool to check for timestamps,
The filename does not correspond to a widely known public asset or a specific viral image with a documented history. However, based on the alphanumeric structure of the name, it is likely a generated filename from a high-volume hosting service or a specific platform. Common Contexts for Such Filenames Technical Analysis (Write-up Template) The filename does not
Note the file type (PNG), its size, and its cryptographic hashes (MD5 or SHA-256) to ensure integrity.