Emily Ferrer.rar -
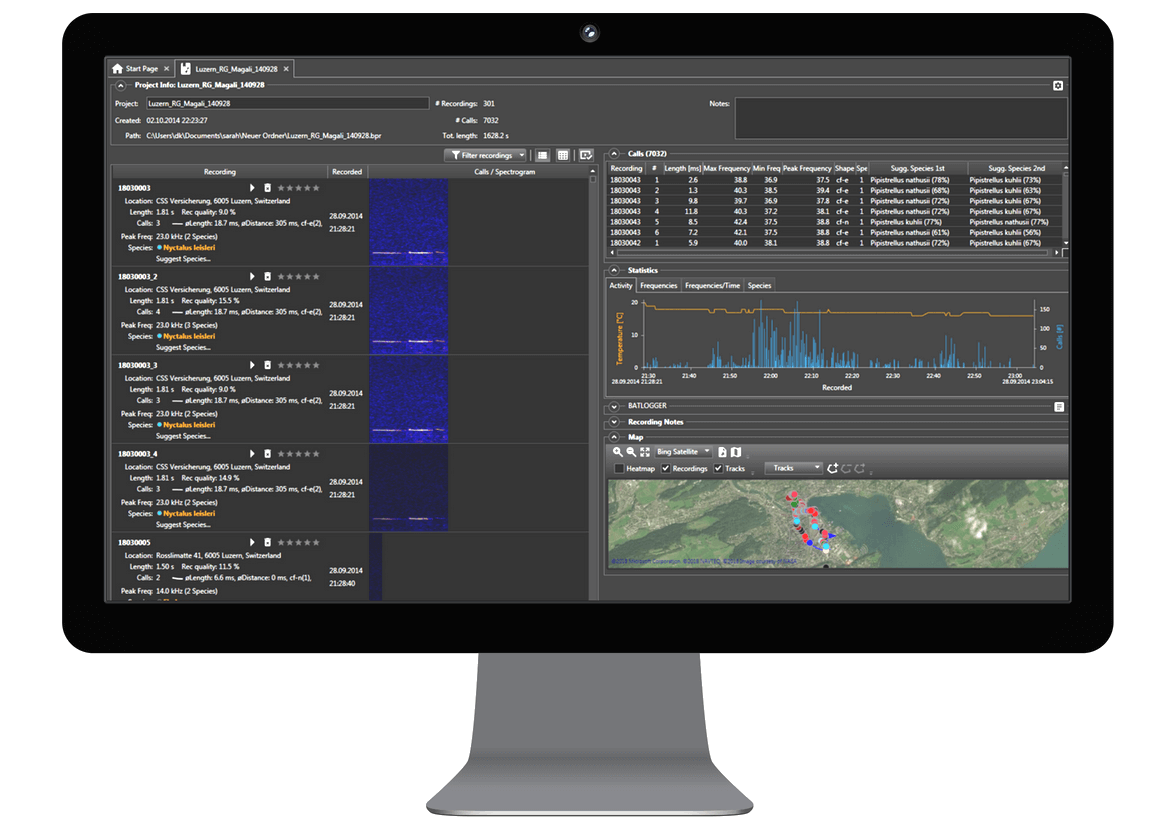
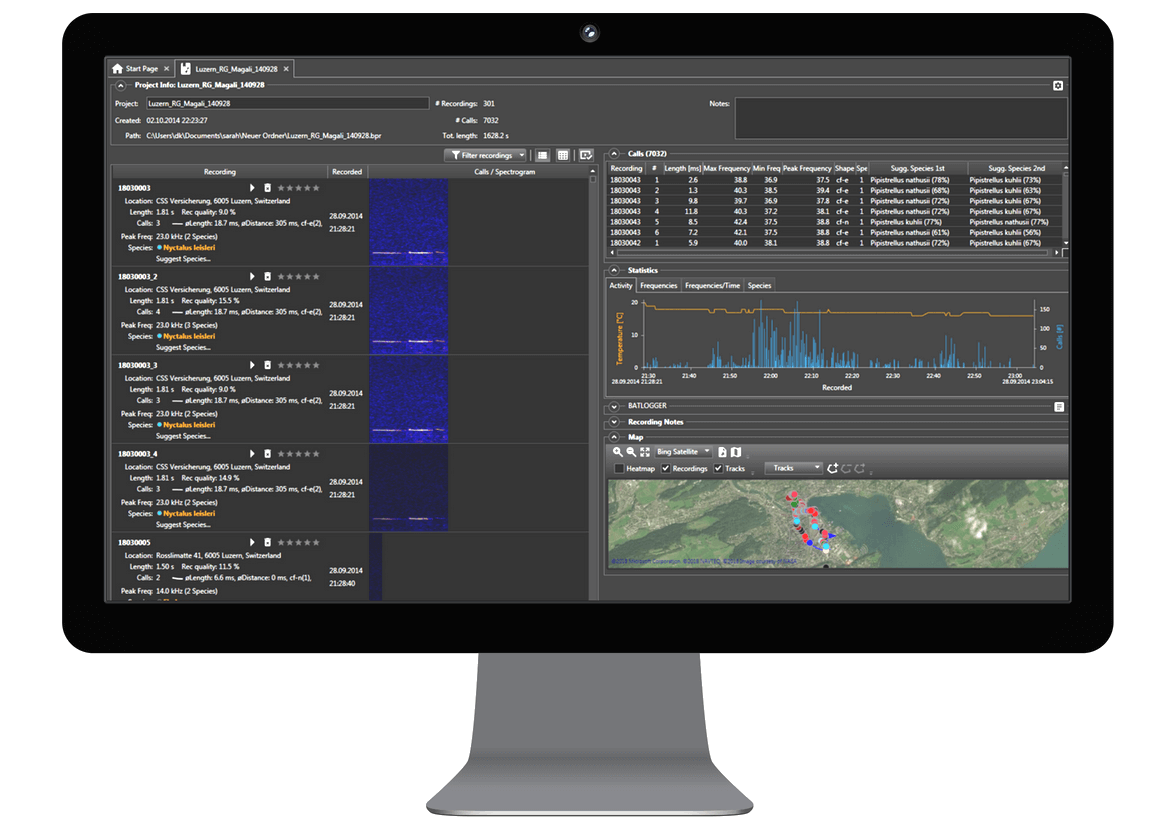
Analyse your recordings
Organize recordings easily and fast
Automatic bat call detection
Listening, viewing and classifying recordings
Automate recurring actions with tasks
Bat species suggestions
Organize recordings easily and fast
Automatic bat call detection
Listening, viewing and classifying recordings
Automate recurring actions with tasks
Bat species suggestions
: In the cybersecurity world, files named after trending figures or leaked "packs" are frequently used as Trojan horses . Users attempting to download the archive often encounter malware, such as keyloggers or ransomware, hidden within the compressed folder. Ethical and Legal Implications
"emily ferrer.rar" is less a specific document and more a symbol of the darker corners of the web. it represents the ease with which privacy can be breached and the persistent risks—both ethical and technical—that come with the consumption of leaked digital media. emily ferrer.rar
: Like many named RAR files in this vein, it often contains non-consensual content, highlighting the ongoing struggle to protect personal data from being weaponized or exploited for "clout" or financial gain in underground digital spaces. : In the cybersecurity world, files named after
: The file exemplifies the "Streisand Effect." Once a collection of data is compressed and distributed under a specific filename, it becomes a permanent artifact of the internet, nearly impossible to fully erase. it represents the ease with which privacy can
: In the cybersecurity world, files named after trending figures or leaked "packs" are frequently used as Trojan horses . Users attempting to download the archive often encounter malware, such as keyloggers or ransomware, hidden within the compressed folder. Ethical and Legal Implications
"emily ferrer.rar" is less a specific document and more a symbol of the darker corners of the web. it represents the ease with which privacy can be breached and the persistent risks—both ethical and technical—that come with the consumption of leaked digital media.
: Like many named RAR files in this vein, it often contains non-consensual content, highlighting the ongoing struggle to protect personal data from being weaponized or exploited for "clout" or financial gain in underground digital spaces.
: The file exemplifies the "Streisand Effect." Once a collection of data is compressed and distributed under a specific filename, it becomes a permanent artifact of the internet, nearly impossible to fully erase.
More information about the software can be found in the Online User Guide.