




Before extraction, the file was integrity-checked to ensure a consistent baseline for analysis. [Insert Hash] SHA-256: [Insert Hash] Size: [Insert Size] MB 2. Extraction & Structural Analysis
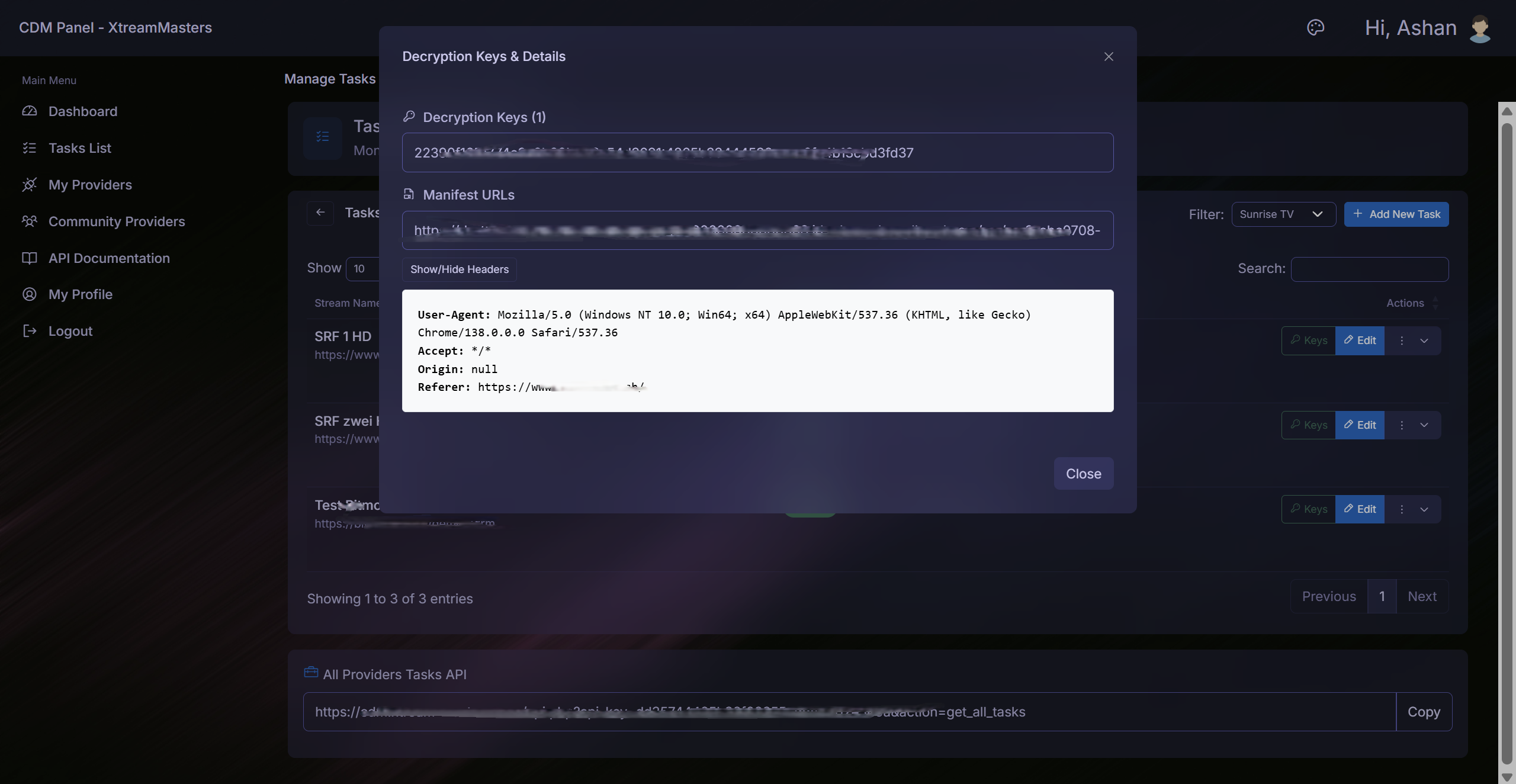
Analysis via ls -la revealed a .hidden_flag file, common in CTF environments. 4. Forensic Findings / IoCs Description 192.168.x.x IP Address Internal C2 listener found in config. malicious_func() Code Snippet Obfuscated logic used to bypass AMSI. HCON{...} The final string required for challenge completion. Conclusion
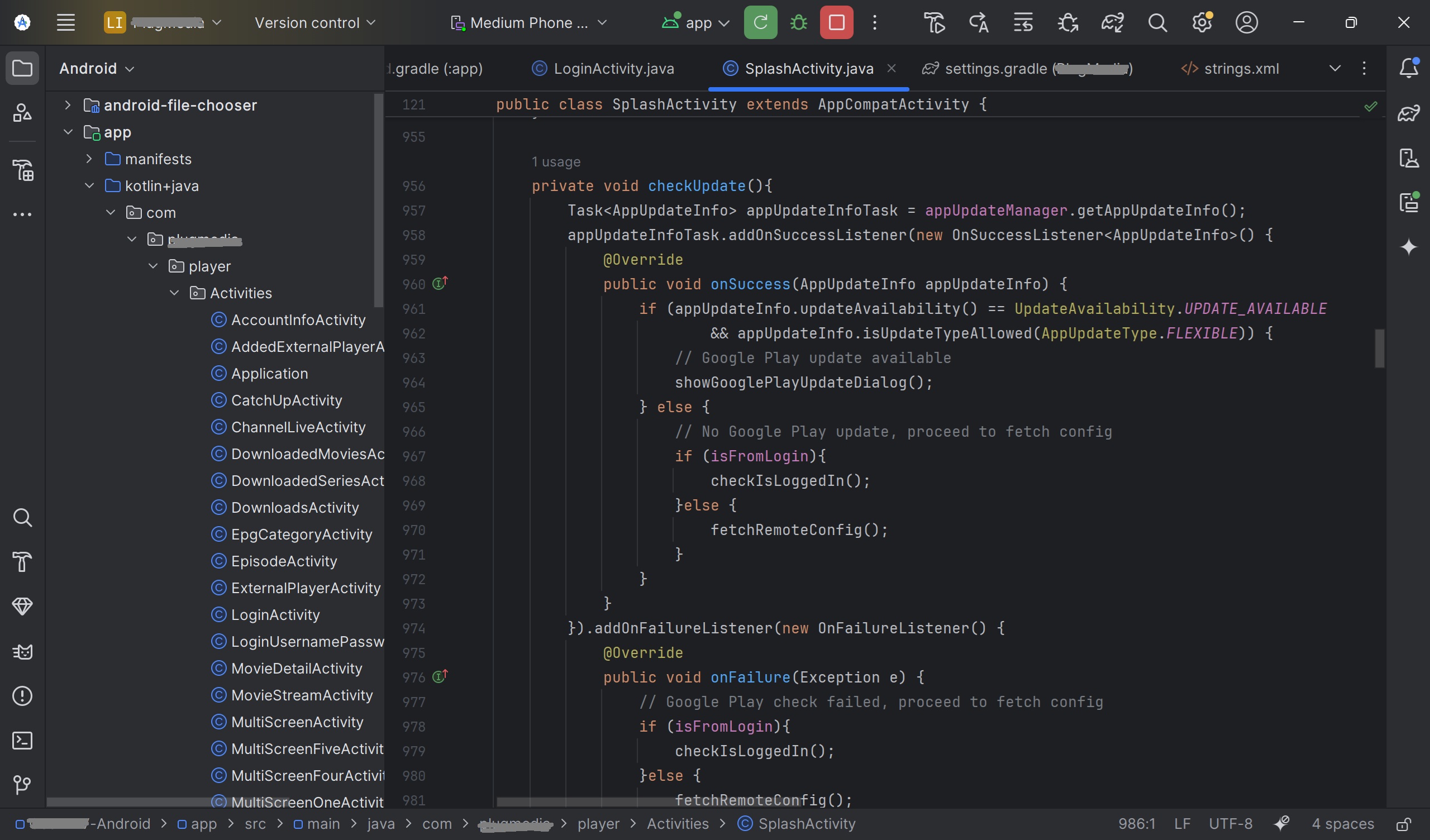
Contained hardcoded IP addresses and API keys, suggesting a specific target environment.
/config/ : Holds .json , .yaml , or .ini files related to tool behavior. /logs/ : Historical data of tool execution.
Based on common cybersecurity patterns, typically refers to a compressed archive associated with Hacker Conference (HCON) materials, specific CTF (Capture The Flag) challenges, or a repository of Hacking Configuration files .
Forensic analysis of a suspected configuration/toolset archive.
We solve real problems that streaming providers face every day.
Every business is different. Our solutions adapt to your needs — from small startups to large providers.
Start small, grow big. Our platform handles traffic spikes without slowing down. No limits on growth.
5+ layers of security, built-in DDoS protection, and encrypted connections. Your content stays safe.
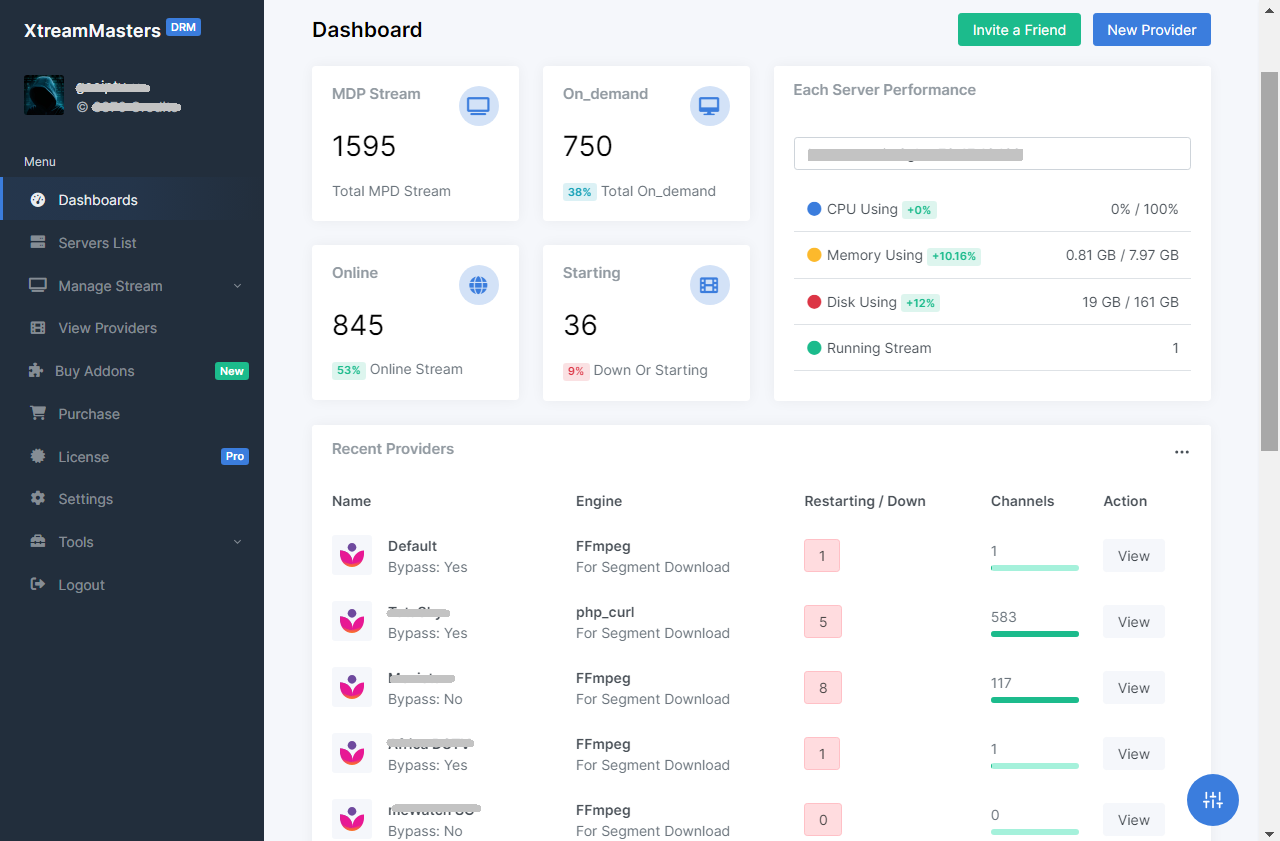
Convert DRM-protected MPD streams to HLS. You bring your own MPD + keys, server or proxy. No content included.
Your own branded IPTV app, ready in 3-7 days. Smart DNS, built-in VPN, all devices supported, and zero downtime with Firebase.
Chrome extension that automatically extracts MPD manifests and Widevine keys. Runs in the background with zero manual effort.
Before extraction, the file was integrity-checked to ensure a consistent baseline for analysis. [Insert Hash] SHA-256: [Insert Hash] Size: [Insert Size] MB 2. Extraction & Structural Analysis
Analysis via ls -la revealed a .hidden_flag file, common in CTF environments. 4. Forensic Findings / IoCs Description 192.168.x.x IP Address Internal C2 listener found in config. malicious_func() Code Snippet Obfuscated logic used to bypass AMSI. HCON{...} The final string required for challenge completion. Conclusion
Contained hardcoded IP addresses and API keys, suggesting a specific target environment.
/config/ : Holds .json , .yaml , or .ini files related to tool behavior. /logs/ : Historical data of tool execution.
Based on common cybersecurity patterns, typically refers to a compressed archive associated with Hacker Conference (HCON) materials, specific CTF (Capture The Flag) challenges, or a repository of Hacking Configuration files .
Forensic analysis of a suspected configuration/toolset archive.